Relevant Products
Single sign-on is available in pro print pro mfp
Supported SAMLv2 SSO providers are Okta and Azure ADFS. Follow the steps described in sections Microsoft Entra Single Sign-On and Okta Single Sign-On / Logout to configure the corresponding SSO.
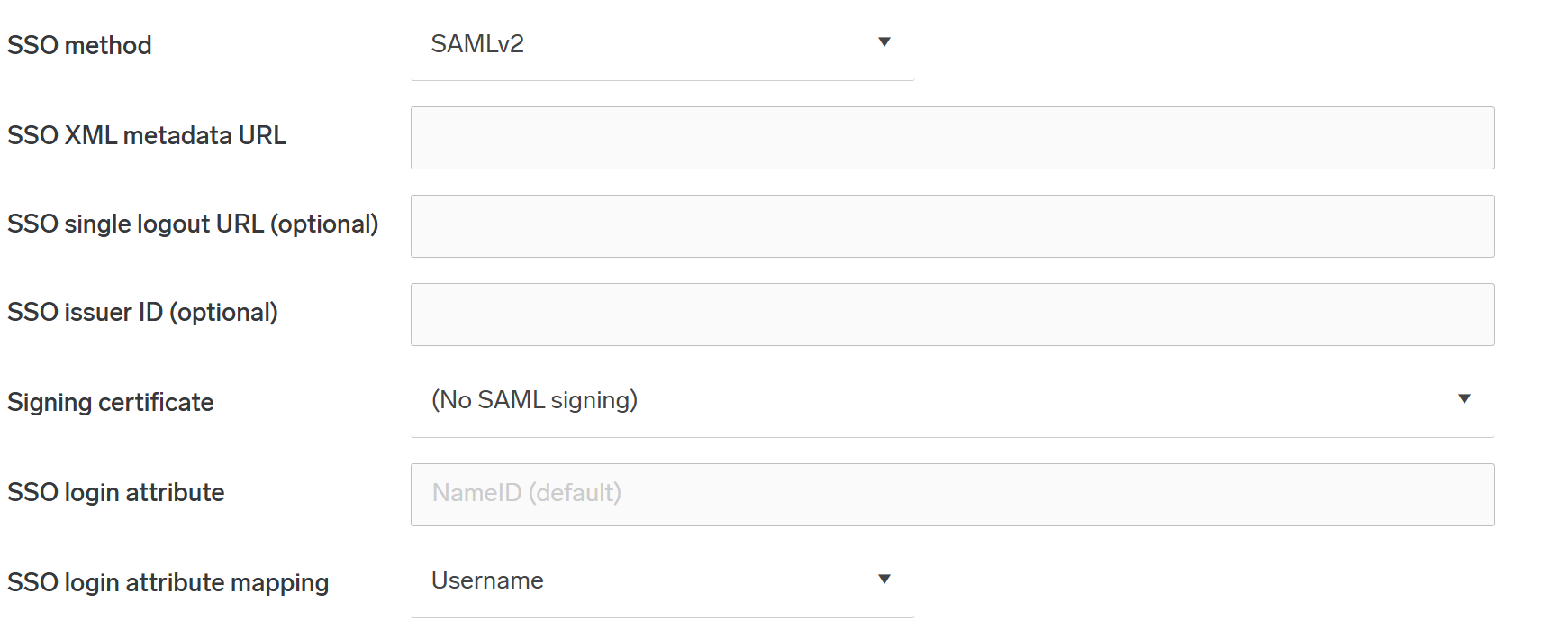
You can configure SAMLv2 Single Sign-On on an account basis in the Users > Single sign-on configuration:
-
In SSO method, select SAMLv2 to enable SSO. Select None to disable SSO. There is no need to add values for the SSO XML Metadata URL if SSO method is None.
SAML will work only if OIDC is disabled in your Authentication providers, or if your Authentication providers use Service Account Authentication in addition to OIDC.
-
In SSO XML Metadata URL, enter the XML metadata URL from the SSO provider's SAMLv2 configuration.
-
In SSO Single Logout URL, enter the URL to the logout endpoint of the SSO provider. This field is optional.
-
In SSO Issuer ID, enter the issuer ID which is sent to SAML SSO provider. If not specified, the URL taken from the browser will be used in the form
https://account:8443/. -
In SSO login attribute, specify the SAML attribute that uniquely identifies the user (e.g.,
uid,email). If left empty, the Identity Provider’s standard NameID will be used instead - this is the recommended and most widely compatible choice. -
In SSO login attribute mapping, select the user attribute to match against the SAML login attribute. Keeping the default (
Username) is recommended.
Notes on the XML Metadata URL:
Instead of an http/s URL the metadata can also be specified with a file URL like file:/{filename} or file:///{filename} where {filename} refers to a file placed in the SAFEQ Cloud installation folder under <install-root>/conf/{filename}.
The file size limit is 1 megabyte. Symbolic links are not allowed. Upon saving the configuration, the specified file is checked for XML validity.
In a cluster setup, this file must be placed on every cluster node.
Identity provider setup guides for Okta
-
Navigate to Applications in Okta and select the one that has SAMLv2 configured.
-
Click the Sign On section.
-
For SSO XML Metadata URL, go back to the Sign On section and copy the URL from Identity Provider metadata.
-
For SSO Single Logout URL, click View Setup Instructions, and copy the URL corresponding to Identity Provider Single Logout URL.
You only have access to the Logout URL if you have enabled Single Logout in the advanced settings of the SAML application.
Okta: https://developer.okta.com/docs/guides/saml-application-setup/config-saml-in-app/
Identity provider setup guides for Azure or Client
-
Navigate to Enterprise applications and select the one that has SAMLv2 configured.
-
Click Single sign-on.
-
For SSO XML Metadata URL, copy the URL from App Federation Metadata XML
-
For SSO Single Logout URL, copy the URL from Logout URL
Make sure that Azure, Client or Okta authentication provider and its corresponding access control are added in SAFEQ Cloud, as well.
